Viewpoint
02.15.18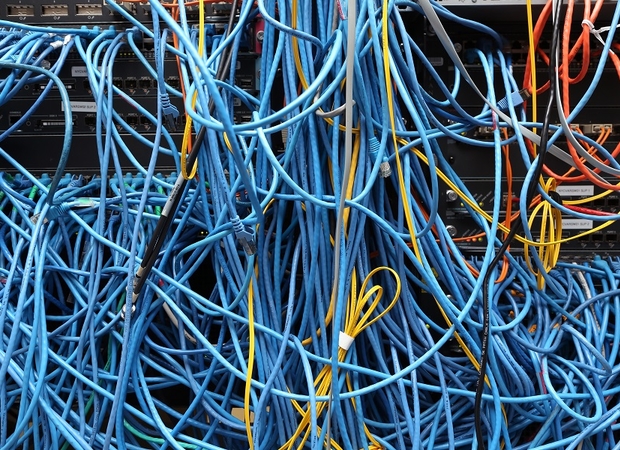
A Clash of Cyber Civilizations
There has been little need for the term “cyber sovereignty” among democratic states: the Internet, by its nature, operates under an aegis of freedom and cooperation. However, as the international system slips away from American unipolarity, a...
ChinaFile Recommends
11.13.17Taiwan Boosts Cyber Defences Against Threat from China
Financial Times
Taiwan’s ruling party is bolstering its cyber defences after hacking attacks that have raised fears that groups linked to the Chinese government plan to influence elections.
ChinaFile Recommends
10.06.17U.S. Confronts China over Suspected Cyberattack as Fugitive Guo Wengui Appears in Washington
Washington Post
A suspected Chinese cyberattack on the website of a prominent Washington think tank drew a complaint from U.S. Attorney General Jeff Sessions this week in a meeting with top Chinese government officials.
China in the World Podcast
09.25.17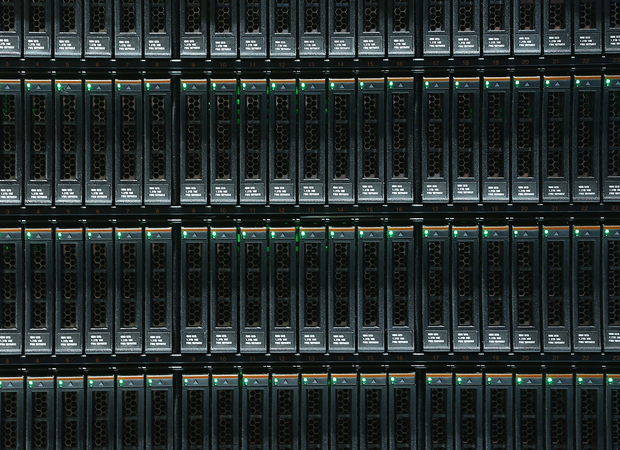
Cyber Norms in U.S.-China Relations
from Carnegie China
The United States and China agreed in 2015 that neither government would support or conduct cyber-enabled theft of intellectual property and committed to working with international partners to identify appropriate norms in cyberspace. Both countries...
ChinaFile Recommends
07.13.17Apple Opening Data Center in China to Comply with Cybersecurity Law
New York Times
Apple said Wednesday that it would open its first data center in China, joining a parade of technology companies responding to growing global demands to build facilities that store online data closer to customers.
ChinaFile Recommends
06.25.17China Has Agreed to Stop Cyberattacks on the Canadian Private Sector, Report Says
Time
China has signed an agreement to stop conducting state-sponsored cyberattacks against the Canadian private sector, the Globe and Mail reported on Sunday, citing an official communiqué.
ChinaFile Recommends
05.17.17China Is Reluctant to Blame North Korea, Its Ally, for Cyberattack
New York Times
China analysts say Beijing will hesitate before directly casting blame on North Korea even if evidence directly ties the North to the attack. Beijing is more likely to single out other actors, particularly the United States, experts say.
ChinaFile Recommends
05.17.17China Is Reluctant to Blame North Korea, Its Ally, for Cyberattack
New York Times
China analysts say Beijing will hesitate before directly casting blame on North Korea even if evidence directly ties the North to the attack. Beijing is more likely to single out other actors, particularly the United States, experts say.
ChinaFile Recommends
05.15.17Tens of Thousands of Chinese Firms, Institutes Affected in WannaCry Global Cyberattack
South China Morning Post
Tens of thousands of Chinese companies and institutions—including several major firms in Hong Kong—have been crippled by a global cyberattack as people returned to work on Monday.
ChinaFile Recommends
04.27.17China Tried to Hack Group Linked to Controversial Missile Defense System, U.S. Cybersecurity Firm Says
A cybersecurity firm in the United States believes state-sponsored Chinese hackers were trying to infiltrate an organization with connections to a U.S.-built missile system in South Korea that Beijing firmly opposes.
ChinaFile Recommends
04.11.17Is Trump Backing Down on China?
Politico
The president last year compared China’s economic behavior to “rape.” Now he says he and Xi are “in the process of getting along very well.”
ChinaFile Recommends
03.20.17How China Is Preparing for Cyberwar
Christian Science Monitor
The U.S. and China have made progress on curbing commercial cyberespionage. Now, the global powers need to set limits when it comes to digital warfare.
ChinaFile Recommends
12.29.16U.S. Charges Three Chinese Traders With Hacking Law Firms
Wall Street Journal
Indictment says the traders bought shares of at least five publicly traded companies before announcements that the firms would be acquired
ChinaFile Recommends
10.12.16Russia May be Hacking Us More, but China is Hacking Us Much Less
NBC News
Chinese hacking has plummeted in the year since China signed an agreement with the Obama administration to curb economic espionage
ChinaFile Recommends
12.02.15China Calls Hacking of U.S. Workers’ Data a Crime, Not a State Act
New York Times
China has acknowledged that the breach of the United States Office of Personnel Management’s computer systems was the work of Chinese hackers.
ChinaFile Recommends
09.30.15U.S. Pulls Spies from China After Hack
CNN
The U.S. suspects that Chinese hackers were behind the breach at the U.S. Office of Personnel Management, which exposed the fingerprints of 5.6 million government employees.
ChinaFile Recommends
09.24.15China's Xi Promises Better Investment Climate, Cyber War Deal Seen
Reuters
Seeking to warm bilateral ties and project a sunny climate for U.S. business, Xi Jinping vowed to cut restrictions on foreign investment.
Conversation
09.22.15
Can the U.S. & China Make Peace in Cyberspace?
Chinese President Xi Jinping arrives in the United States today on his first state visit. Xi will address a group of American business leadersin Seattle. High on their list of concerns about trade with China is cyber hacking, cyber espionage and...
ChinaFile Recommends
07.06.15Hillary Clinton Says China Hacks into “Everything that Doesn’t Move”
Quartz
The Democratic presidential candidate accused Chinese hackers of stealing “huge amounts of government information.”
ChinaFile Recommends
06.16.15Former CIA Chief Says Government Data Breach Could Help China Recruit Spies
Wall Street Journal
Retired Gen. Michael Hayden calls records a ‘legitimate foreign intelligence target’.
ChinaFile Recommends
06.12.15Chinese Hackers Circumvent Popular Web Privacy Tools
New York Times
The attackers compromised websites frequented by Chinese journalists as well as China’s Muslim Uighur ethnic minority.
ChinaFile Recommends
06.05.15China in Focus as Cyber Attack Hits Millions of U.S. Federal Workers
Reuters
Hacks possibly compromised the personal data of 4 million current and former federal employees.
ChinaFile Recommends
04.16.15Why Do the Chinese Hack? Fear
War on the Rocks
To ensure its survival, the Chinese Communist Party has decided that it must control the Internet.
ChinaFile Recommends
04.13.15China Accused Of Decade Of Cyber Attacks On Governments And Corporates In Asia
TechCrunch
“There’s no smoking gun...,but all signs point to China” Bryce Boland told TechCrunch.
ChinaFile Recommends
03.19.15China (Finally) Admits to Hacking
Diplomat
An updated military document for the first time admits that the Chinese government sponsors offensive cyber units.
Viewpoint
02.19.15
Beijing Touts ‘Cyber-Sovereignty’ In Internet Governance
It has been a difficult few weeks for global technology companies operating in China.Chinese officials strengthened the Internet firewall by blocking the use of virtual private networks (VPNs), reasserted demands that web users register their real...
ChinaFile Recommends
12.22.14Opinion: In Response to Sony Hack, U.S. Should Focus on China Not North Korea
Christian Science Monitor
Mr. Obama’s punt is not a big surprise as there simply are no good options for responding to North Korea. How do you calibrate a “proportional response” when not countering a military attack but one that targets freedom of expression?
ChinaFile Recommends
12.22.14China Said to Probe U.S. Claims of North Korea Role in Sony Hack
Bloomberg
The dispute between the U.S. and North Korea is escalating after hackers forced Sony to pull a comedy movie about the assassination of North Korean leader Kim Jong Un, exposed Hollywood secrets, and destroyed company data.
ChinaFile Recommends
12.19.14U.S. Blames North Korea for Sony Cyber Attack, Vows ‘Consequences’
Reuters
It was the first time the United States had directly accused another country of a cyber attack of such magnitude on American soil and sets up a possible new confrontation between longtime foes Washington and Pyongyang.
Reports
12.03.14
Warring State: China’s Cybersecurity Strategy
Center for a New American Security
Research Associate Amy Chang explores the political, economic, and military objectives of China’s cybersecurity apparatus; reveals drivers and intentions of Chinese activity in cyberspace; and analyzes the development of Beijing’s cybersecurity...
ChinaFile Recommends
07.15.14Chinese Hackers Extending Reach to Smaller U.S. Agencies, Officials Say
New York Times
After years of cyberattacks on the networks of high-profile government targets like the Pentagon, Chinese hackers appear to have turned their attention to far more obscure federal agencies.
ChinaFile Recommends
05.21.14China Accuses U.S. of Hypocrisy Amid Charges of Economic Espionage
Al Jazeera
Unresolved allegations that the U.S. National Security Agency spied on a Chinese telecoms giant Huawei have resurfaced amid growing anger from Chinese officials over accusations that the PLA hacked American databases.
Conversation
05.19.14
Is This the Best Response to China’s Cyber-Attacks?
On Monday, the United States Attorney General Eric Holder accused China of hacking American industrial giants such as U.S. Steel and Westinghouse Electric, making unprecedented criminal charges of cyper-espionage against Chinese...
ChinaFile Recommends
05.19.14Department of Justice Indicts Chinese Hackers: What Next?
Council on Foreign Relations
The US indicted five Chinese military officers for cyberspying, but the Snowden revelations about alleged NSA activities make it hard to build support for diplomatic efforts from the rest of the world.
ChinaFile Recommends
04.06.14U.S. Tries Candor to Assure China on Cyberattacks
New York Times
The Pentagon’s emerging doctrine includes defending against cyberattacks on the United States and also using its cybertechnology against adversaries, including the Chinese.
ChinaFile Recommends
01.22.14China Suffers Massive Internet Outage, Analysts Suspect Hackers
CNN
The state-run China Internet Network Information Center blamed the blockage on a “malfunction in root servers.”
ChinaFile Recommends
05.17.13U.S. Blames China’s Military Directly for Cyberattacks
New York Times
Until now the administration avoided directly accusing the People’s Liberation Army of using cyberweapons against the United States in a deliberate, government-developed strategy to steal intellectual property and gain strategic advantage.
ChinaFile Recommends
04.30.13Mandiant: No Drop In Chinese Hacking Despite Talk
WSJ: China Real Time Report
The only change, Mandiant’s Chief Security Officer said, has been a noticeable drop in cyber attacks from Unit 61398, a group within the People’s Liberation Army that Mandiant accused in February 2013.
ChinaFile Recommends
04.26.13U.S. Eyes Pushback On China Hacking
Wall Street Journal
Current and former officials said the offensive shift turned on two developments: new intelligence showing the Chinese military directing cyberspying campaigns, and a sudden change in U.S. companies’ willingness to acknowledge Chinese...
ChinaFile Recommends
04.19.13What Kerry Should Tell China
Foreign Policy
On April 13, 2013, when John Kerry pays his first visit to China as the U.S. secretary of state, North Korea will be at the top of his agenda, with Iran’s nuclear program and cyberattacks also extremely important.
ChinaFile Recommends
04.11.13Beijing Opposes U.S. Rule On Technology Imports
Reuters
The new provision following recent cyberattacks requires NASA, as well as the U.S. Justice and Commerce Departments, to seek approval from national law enforcement officials before buying information technology systems from China.
ChinaFile Recommends
03.22.13South Korea Says China Hack Link A ‘Mistake’
BBC
Hackers can route their attacks through addresses in other countries and intelligence experts believe that North Korea routinely uses Chinese computer addresses to hide its cyber-attacks.
ChinaFile Recommends
03.21.13As Hacking Continues, Concerns Grow That Chinese-Americans May Suffer
International Herald Tribune
An interview with prominent Chinese-American legal scholar about the recent hacking issue and Chinese-Americans role in offsetting potential negative misconceptions about the community.
ChinaFile Recommends
03.14.13China Hacker’s Angst Opens A Window Onto Cyber-Espionage
Los Angeles Times
A P.L.A. hacker’s blog is discovered, providing a rare peek into the secretive hacking establishment of the Chinese military, in what is believed to be by far the world’s largest institutionalized hacking operation.
ChinaFile Recommends
03.08.13The Brutality Cascade
New York Times
As China's economic and defense tactics appear to become more and more successful, David Brooks expects other countries' policies will start to resemble them, whether or not they run counter to our principles.
ChinaFile Recommends
03.01.13Cyber Menace: Digital Spying Burdens German-Chinese Relations
Spiegel Online
European Aeronautic Defense and Space Company’s (EADS) firewalls have been exposed to attacks by hackers for years, but now company officials say there was “a more conspicuous” attack a few months ago.
ChinaFile Recommends
02.26.13What China’s Hackers Get Wrong About Washington
Washington Post
Chinese hackers believe the most pervasive of of all Washington legends: that everything that happens in D.C. fits into somebody’s plan. Because in China, it would be like that. Not in our nation’s capital.
ChinaFile Recommends
02.26.13In Cyberspace, New Cold War
New York Times
The early 2013 cyberattacks and the U.S. government’s response illustrate how different the cyber-cold war between the U.S. and China is from the more familiar superpower conflicts of past decades.
Media
02.22.13
Complaints, Nationalism, and Spoofs
This week, United States government and American media charges of Chinese cyberattacks have led to a variety of responses from netizens across China. On February 19, a CNN camera crew tried to shoot video of the twelve-story military-owned building...
ChinaFile Recommends
02.22.13Chinese Hackers Are Getting Dangerously Good At English
Foreign Policy
Chinese hackers are getting dangerously good at tricking users into clicking on what are known as “phishing emails” -- messages with links or attachments that seem innocuous, but actually dump spyware on recipients'...
ChinaFile Recommends
02.22.13ChinaFile Recommends
02.22.13China, Its Hackers, And The American Media
Atlantic
While the story presented fresh evidence of Chinese hacking, the aftermath presents more questions than answers about U.S.-China relations, as well as the connection between U.S. media and Chinese government.
ChinaFile Recommends
02.22.13China Says Army Is Not Behind Attacks In Report
New York Times
Geng Yansheng, a spokesman for the Ministry of National Defense, says “The claim by the Mandiant company that the Chinese military engages in Internet espionage has no foundation in fact.”
ChinaFile Recommends
02.22.13What Do We Make Of The Chinese Hacking?
Atlantic
Is this recent hacking really something new? Or merely our "threat inflation,"* cued both to the impending sequestration menace and February 2013 SOTU mentions of new efforts in cyber-security?
ChinaFile Recommends
02.22.13Authorities Reject Cyber Crime Accusation
Global Times
The report does not reflect the facts and is not professional, and the PLA has never supported any cyber espionage activities, China's defense ministry said on its official website in response to the accusation.
ChinaFile Recommends
02.22.13U.S.: Hacking Attacks Are Constant Topic Of Talks With China
McClatchy
Obama administration officials acknowledged that China’s involvement in cyber-attacks is a near-constant subject of conversation between the nations’ officials but that there have been few signs that China is willing to stop the attacks.
ChinaFile Recommends
02.21.13Malware Attack On Apple Said To Come From Eastern Europe
Bloomberg
At least 40 companies including Apple Inc., Facebook Inc. and Twitter Inc. were targeted in malware attacks linked to an Eastern European gang of hackers that is trying steal company secrets.
ChinaFile Recommends
02.20.13A Look At Mandiant, Allegations On China Hacking
Associated Press
An introduction to Mandiant, the details of its recent report on alleged government-affiliated Chinese hacking, why the report is significant, and potential backlash from the report.
ChinaFile Recommends
02.20.13Chinese Army Unit Is Seen as Tied to Hacking Against U.S.
New York Times
An unusually detailed 60-page study tracks for the first time individual members of the most sophisticated Chinese hacking group to the doorstep of the military unit’s headquarters.
Media
02.20.13
On China’s Twitter, Discussion of Hacking Attacks Proceeds Unblocked
As The New York Times reported yesterday evening, U.S.-based cybersecurity firm Mandiant has just released a deeply troubling report called “Exposing One of China’s Cyber Espionage Units.” The report alleges wide-spread hacking sponsored by the...



